SU25 – A Discussion
There is already a post in this blog which talks about the SU25 transaction. However while recently working on a upgrade, it occurred to me that the information presented was too broad and might not answer a lot of the doubts that a security analyst might face when actually tasked to complete the full post SU25 execution. I do not claim that this post will answer all the question but it does go into more depth about the thinking that should go into the post upgrade activities. This is all the more important as when done wrong, the SU25 activity has potential to reduce the check indicators and roles for a SAP system to junk!
A service pack upgrade is a recurring event in any SAP project. Typically SAP introduces new applications as part of service packs. It is also possible that SAP re-writes the code around existing SAP applications. Any of these changes can introduce new security checks in the code and which need to be added into the security roles. The SAP provided tools for security upgrades are accessed by using the SU25 transaction.
Going into SU25 after an upgrade will reveal a screen similar to the one below
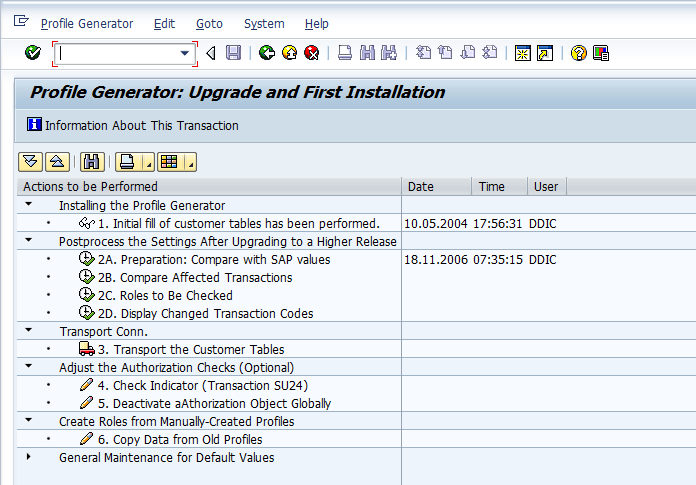
We never run Step 1 after an upgrade. Step 1 is only meant to be run after a new SAP installation and will copy all data from the SAP tables to the customer tables and overwrite everything.
For an upgrade, we start the SU25 activities by running step 2A. This compares the data in USOBT and USOBX with USOBT_C and USOBX_C. If SAP determines that there is no conflict between the SAP proposed values with the values maintained by the customer, it goes ahead and copies the data to the customer tables. For the transactions where it determines that SAP proposed values conflict with customer values, it proposes that we compare and manually adjust the values in Step 2B.
After 2A, we now run Step 2B and manually compare the list of transactions where the list of SAP proposed check indicator and default values is different from the values maintained by us. We go through all affected transactions one by one and either accept SAP proposed values or keep the values maintained by us.
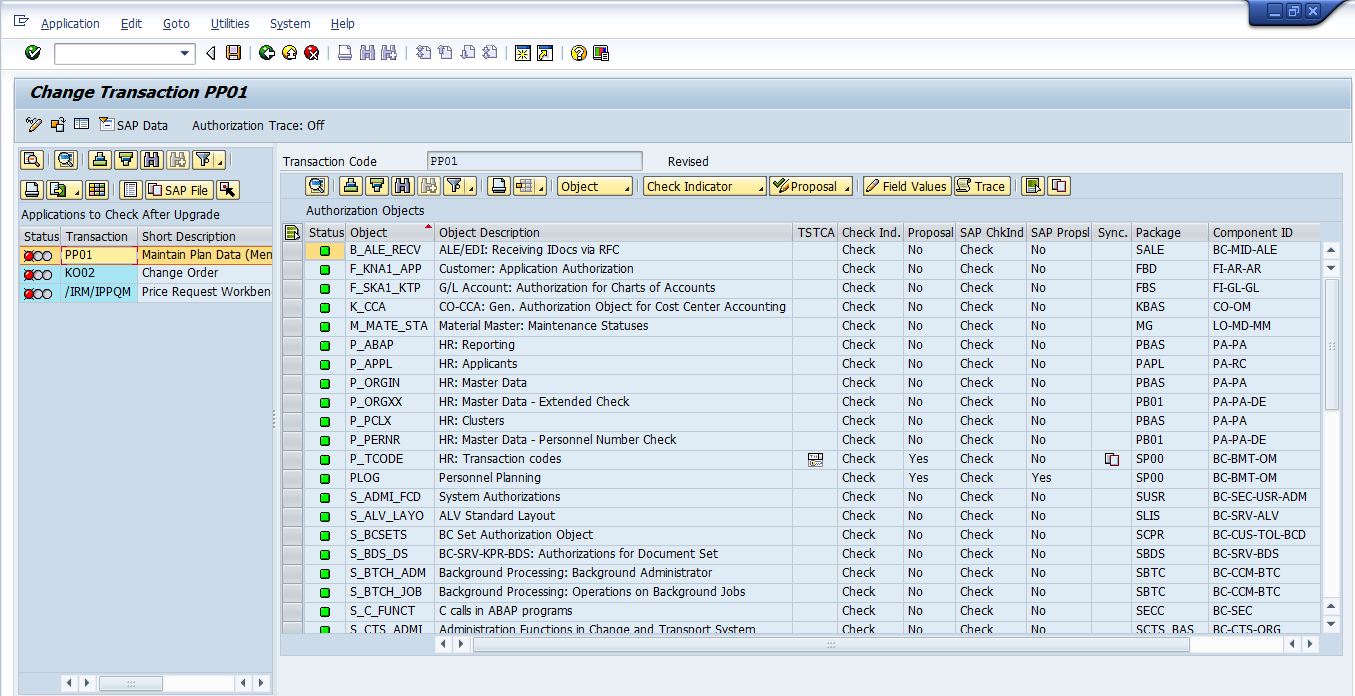
In most cases, we would keep the customer values unless there is an overwhelming need to change it to the proposed values. The most important case would be to look for cases where SAP is proposing more security than what we have in the system (for example SAP proposal is for check whereas customer proposal is for do not check). Once we are through with the entire list of affected transactions we are ready to go into the next step 2C to look at the roles affected by the changes to SU24 data. At this point it is advisable to take a backup of the USOBT_CD and USOBX_C change log tables so that we have an idea of the values changed as part of SU25 activity.
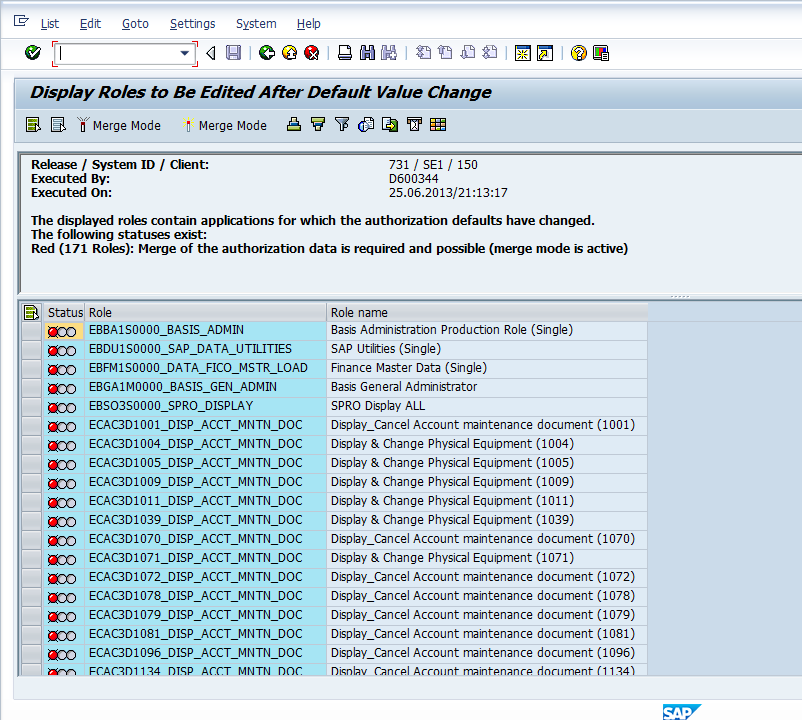
In Step 2C, SAP provides us a list of all roles which have transactions in their menu which have SU24 data updated as part of the SU25 activity.
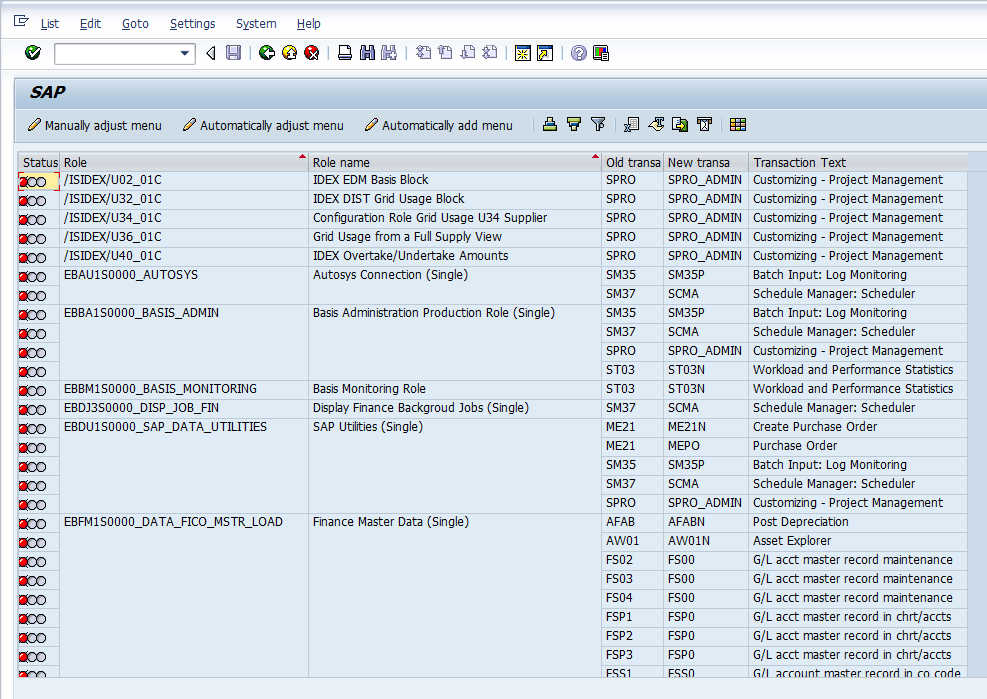
The Step 2D is optional and mainly meant to check if SAP has introduced new transactions in place of any existing transactions.
The last mandatory step in the SU25 process is to run Step 3 and transport the customer tables. This was the latest customer tables are transported into all the successive environments in the landscape. The transport of the tables should be followed by a transport for all the roles which were generated as part of Step 2C
Downloading/Uploading SU25 Data
As already discussed , the SU25 transaction over-writes the customer tables with SU24 data, USOBX_C and USOBT_C with the SAP provided data in USOBX and USOBT. As a precaution we would like to take a backup of the customer tables and also a backup of the SU24 data using the RSU22DOWN. The downloaded file from RSU22DOWN can be later re-uploaded into the SAP system to go back to the earlier customer defaults.
Hello Aninda,
Which is really help full.
Thank you for providing this valuable information.
I have one more doubt which is there any way to mass upload the users?
Please clarify me on the query.
Thanks In Advance!
Regards,
Siva V.
LSMW, SECATT, BAPIs
Is there any way to mass upload users?
Regards,
Siva V.
Hi Aninda,
How does report RSU22DOWN helps in going back to earlier version? I ran this program in my system and ?I get nothing as an output.
The RSU22DOWN program is meant to download the SU24 tables to a text file. If its not downloading you might not be following the correct steps. Do a web search. The SAP help article on how to use the program is in the first few search entries.
Hi Aninda, There seems to be no difference between SU25 and SU26. Why is that we even have SU26 transaction? Thanks in advance.
hi
aninda
what is the t-code su26
pls give answer asap
thanks
I have not had to use it yet. The functionality seems to be similar to SU25. Would be glad if someone who has had experience using it could comment.
Hi Annada,
Thanks for your information
I have one doubt, are these roles need to be generated which are showing in RED status before transporting?
Thanks
Madhu
You should not transport roles with unmaintained values for authorization objects. So just ensuring that roles are green won’t be enough as a role with unmaintained values can still be generated.
Hi Aninda
Need small info.
I have executed tc.de Su25 Sepn 2A to 2D in ECC 6.0 system and then remediated the affected roles with user assignment generated from Step 2C in DEV box. Now the client says do not transport the changes ie Step 3 but transport the affected roles in QA system. My questions is will the remediated roles works in QA system without the customer table? Please reply
Thanks
Saur
Hey Man – Can you reply fast?
The customer tables need to be transported as well. Otherwise the full impact of the SU25 changes will not be experienced in QA or Prod environments.
Hi Aninda
Need one info.
After executing SU25 Steps 2A to 2D in DEV box of ECC 6.0 system, I got list of affected roles. I remediated those affected roles and they are now ready to be transported in QA system. My question is that client asks us not to executed Step 3 and transport the customer table data in QA system. Is it ok to move the remediated roles in QA system without transporting the customer table data?
Thanks
Saur
Hi,
Two questions regarding step 3. In ecc system we changed su24 table manually and moved the changes to quality but did not use step 3.Quality testing is almost completed should I transport changes through step 3 and if done it will impact in quality?
Scenario-2 BW system no changes in su24 so so did not moved to quality.Testing in quality is completed should I move the changes through step 3??
If already moved the custom tables manually, re-transporting them through SU25 is not necessary. You can verify that the latest changes are in QA by comparing the table values from DEV.
Hi Aninda,
Great resource you have here!
I just had a question about SU25 step2A. Would you happen to know if step 2A transfers data?
After executing step 2A, it looks as though the data was altered in tables USOBT_C and USOBX_C. After doing some research, I thought 2A just compared the tables USOBX and USOBT with USOBX_C and USOBT_C.
Any input would be appreciated.
Thanks in advance!
Nathan
Step 2A is not a read only step but does write data into the custom tables. If after running the comparison between standard and custom table values, if SAP determines that there is a conflict only then are these are displayed in 2B, otherwise the updates occur in 2A. This post talks at length on what’s happening behind the scenes.
Hi Aninda,
I am new to SAP HR security. Happen to view your post during google search. Your post are wonderful. I would like to clarify related to SAP HR. I am aware that HR and BASIS object cant be changed thru SU24. just want to know what happens to SAP HR object after an upgrade or patches takes place..
Thanks in Advance
Hello,
I need document on SCM APO implementation can anyone help me on this
Thank you.nice explanation